What is JQuery?
JQuery is a JavaScript library which can simplify your work with code. It is a powerful tool but vulnerable to Cross Site Scripting and other vulnerabilities, except starting from version 3.5.0. In this article we will talk about reflected XSS vulnerability in older versions of JQuery library.
How can it be compromised?
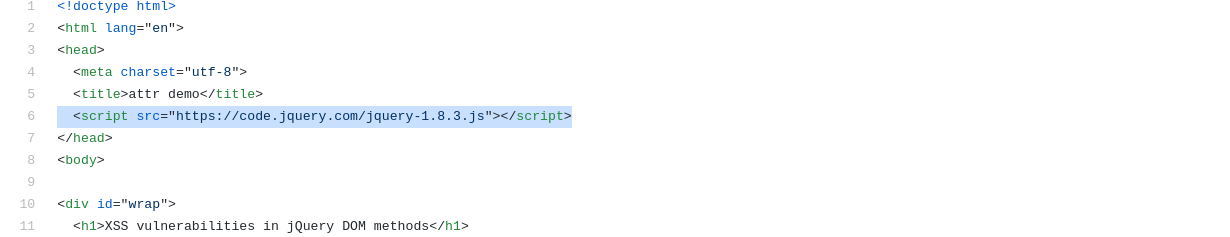
First thing we need to check the JQuery version, in this example we have version 1.8.3 which is vulnerable:
<script src="https://code.jquery.com/jquery-1.8.3.js"></script>
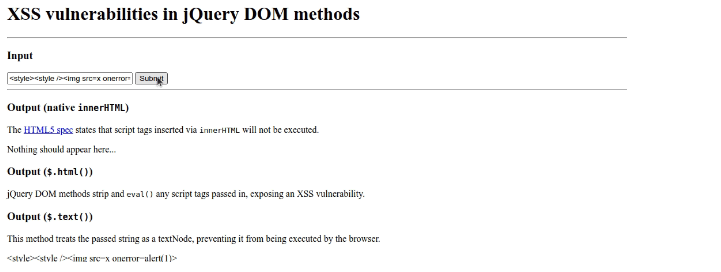
After our check we can start the XSS attack. In this example we will alert “1”. We have HTML form with input field:
<form>
<input id="test" placeholder="Enter malicious input here" size="30" value="INPUT" />
<input type="submit" value="Submit" />
</form>After injecting our XSS payload in the input field and submitting we will see an alert with description “1” on the webpage.
This vulnerability was fixed with the new JQuery version (3.5.0). So, if you update JQuery library to the latest version (for example 3.6.0):
<script src="https://code.jquery.com/jquery-3.6.0.js"></script>
This code (XSS ) cannot be executed:
<style><style /><img src=x onerror=alert(1)>
In this article we have an example of reflected cross site scripting vulnerability. Attacker can modify the link with malicious code to the website and it will be executed in the victim's browser, as a result sensitive information can be compromised or custom operations performed while impersonating the user identity.
How to prevent it?
In this case it is a good idea to update JQuery library to the latest version as the developers have fixed this issue with XSS vulnerability.
Sources: